Here today, yongeTOmorrow (pt.1)
Posted on April 16th, 2026 – Comments Off on Here today, yongeTOmorrow (pt.1)Perhaps you think that I’m engaging in cynical hyperbole but I assure you that I’m not: City Hall is going to demolish the most iconic section of Yonge Street in downtown Toronto. Sure, they plan to rebuild it again afterwards but it’ll look and feel much different — the old Yonge Street of today will be gone.
The push for this started back in the summer of 2011. At the time it was considered a long shot since the concept was mainly just a pedestrian-friendly facelift put forward by gay, lefty-pinko junior Councillor Kristyn Wong-Tam and Pride-avoiding, right wing, penny-pinching, newly-elected businessman Rob Ford (remember him?) who, it may surprise you to learn, wasn’t really a big fan of walking or running, wasn’t onboard. So the idea simmered on the back burner for about a decade.
At some point it was determined that a length of Yonge would need century-old water mains replaced and, since this requires wrecking and rebuilding the street anyhow, the proposal resurfaced, congealing early in 2021 into something called yongeTOmorrow. I don’t know to what extent the Wong-Tam’s plan has morphed over the years but right now City Hall is eyeing the portion between Queen Street and College/Carlton for the first phase of a Yonge makeover.
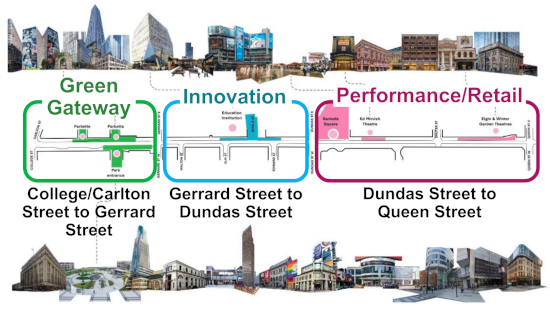
As of 2024, the most current design by engineering firm Parsons splits up the initial stretch into three themed sections.
Each of these sections are clustered around what the project calls Anchors, defined as “existing landmarks that contribute towards the identity of Yonge Street.”
While the “Green Gateway” is indeed quite green and the “Performance/Retail” portion is also aptly named, I’m hesitant to use the word “Innovation” for its designated section simply because of that area’s proximity to Ryerson/Metro University. Some of their innovations are dubious if you ask me.
Nevertheless, the practical result of the current plan would be the reduction of the street to one lane in each direction, to be shared by both motor vehicles and bikes. The design includes “Designated Short-Term Areas”, presumably short bits where the road flares out to two lanes for drop-offs/pick-ups. Along with this there’s a speed limit reduction to 30 km/h.
The resulting space will be used to widen sidewalks and include strips with greenery and street furniture, sort of like permanent curb lane cafés à la CaféTO. How much of these strips will be for public use and how much will be designated for adjoining businesses (i.e. private, à la CaféTO), remains to be seen.
Tenders for the construction are expected to begin in 2030 and construction itself is expected to take about 5 years — with the proviso that this is dependent on the progress of Doug Ford’s unspoken tribute to his late brother Rob, the Ontario Line.
If the timelines of something like Union Station Revitalization or the new St. Lawrence North Market are anything to go by, it’ll be a miracle if any projected costs haven’t at least doubled by the time shovels are in the ground, or whatever futuristic digging implements will be in use at the time, which will likely be 2040 at the earliest.
That gives us at least 14 years to experience and capture the downtown Yonge Street of future yesteryear.
The design is still undergoing public review and there’s a scheduled public drop-in event next Tuesday at the central YMCA that, “will provide an opportunity to view the project information panels and speak with members of the project team one-on-one.” In other words, if you want to meet some of the people who will eventually be responsible for astronomical cost overruns, extensive delays, and assorted disruptions to the surrounding community, this might be the event for you.
Maybe I’m just trafficking in hyperbolic cynicism. Maybe they’ll have coffee and doughnuts. Whatever the case, a “pt.2” is inevitable.