I’ll explain
Posted on June 27th, 2014 –
Sorry for the interruption.
Hopefully it’s at least revealing to know that even as I write these lines I’m in a precarious situation (whatever income I do have is entirely spoken for), so please don’t mistake me for some well-to-do bohemian philosopher. And I know I’m not getting that seized money back so now I have to decide which bills aren’t getting paid.
But let’s not dwell.
I’d like to explain what I was getting at earlier. Because I really do have faith in something, and that something is technology.
Oh, don’t get me wrong — I know my computer isn’t going to hug or feed me tomorrow. It’ll barely keep me warm in the winter. In the summer, it does a shitty job of keeping me cool. It never encourages me, and frankly, it barely acknowledges my presence. But it does provide access to something: digital privacy and anonymity.
Privacy
Of course government surveillance means that my expectations should be restrained, but based on everything I know about encryption, surveillance, and data collection, I believe that what governments are doing amounts to basically data warehousing — until they can figure out a way to crack some of the heavily encrypted stuff. And that’s proving very challenging.
So that’s a great place to start, for example, by learning how to encrypt your email. See if your friends can read them, just for shits and giggles. This took me a few moments to set up for the first time so I’d recommend giving yourself some time to absorb the instructions.
Don’t rush — misunderstanding is often as dangerous as sheer ignorance. The Khan Academy does a great job of explaining how you and another person can communicate privately when you’re constantly being listened in on (the ideas are initially explained using colours — no math!):
If you stuck around for the math in the second half, you may have noticed that this (the big number stuff), seems like something computers would be good at. Right? And the underlying concepts have many real-world analogues too.
One might opine that it’s almost as if God weaved these mathematical tidbits into the fabric of the universe for us to discover and use.
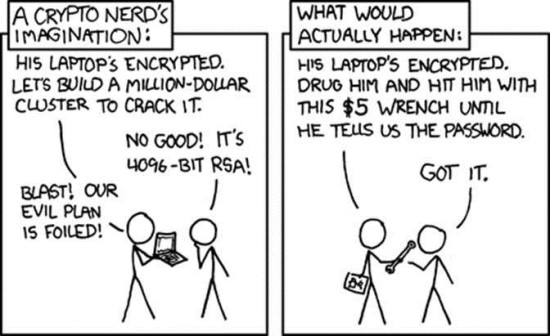
If you’re not really familiar with practical encryption, it’s a good idea to peruse the more general material. Take your time because encryption by itself isn’t enough. There are many ways that you can inadvertently reveal your personal information (stuff like writing your password on a sticky on your work PC), so an education in encryption is 50% technology and 50% human. Keep in mind that security is often also compromised via “rubber-hose cryptanalysis“.
So we’re also aiming for is anonymity. With everything now living in “the cloud” (a fancy term for “somebody else’s computer”), our anonymity can be ephemeral. If we can be both private and anonymous (eavesdroppers know neither what’s being said nor who’s saying it), then maybe there’s a chance that private exchanges between individuals (outside of the government’s gaze), are possible.
The privacy is done through encryption. Anonymity is provided by something like the Tor network.
Anonymity
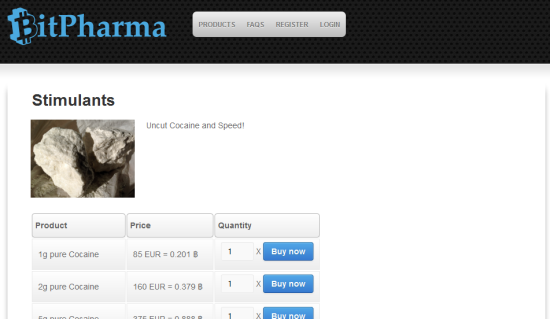
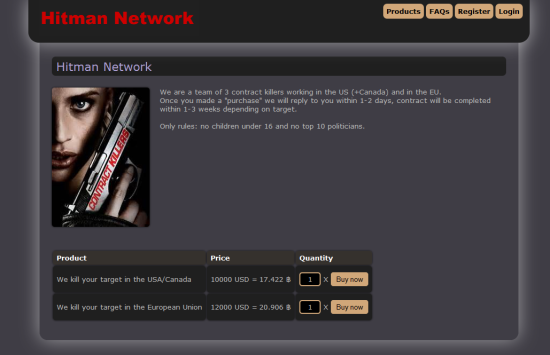
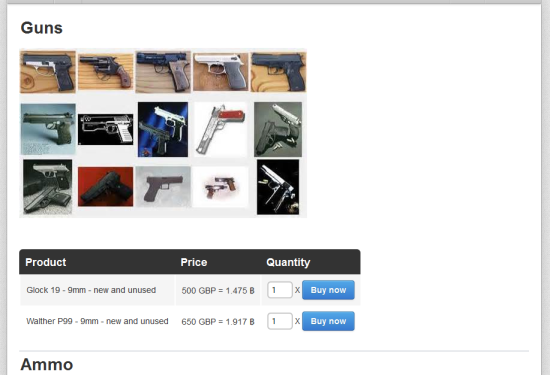
Tor is the current crème de la crème of what is lovingly called “The Dark Net”. You know…
Yup, this stuff is out there. Big shock. I mean, don’t we know by now that when something is illegal, a black market will spring up? So law helps to stoke the fires, and government swoops in with a leaky, overpriced, corrupt bucket of water. And that such a market should exist online is equally as un-shocking. That doesn’t mean Tor is all bad — it’s all in how you use it. All it’s designed to do is to keep you anonymous.
How qualified am I to be dolling out Tor advice? Well, I wrote the library for controlling and communicating through Tor using Adobe Flash and AIR, so I’d say I’m fairly well qualified.
On this topic, I’ve written a pretty buggy and totally not-ready-for-public Tor application that you can play with (it launches whatever version of IE, Chrome, or FireFox that you may have installed in “Tor mode”): http://www.torontocitylife.com/downloads/BreakOutBox.exe
I’ll be releasing this as open-source as soon I’ve cleaned it up a bit. Feel free to write me to get your hands on it earlier, or with any of the obvious (or not so obvious) problems you encounter.
Update (July 1): I urge caution when using BreakOutBox at this point — it doesn’t correctly reset your browser’s proxy settings so you’ll probably have to reset them yourself after closing the program. I’ll try to have this fixed in the next version. Also, if you downloaded BreakOutBox before July 1st, it won’t work (I forgot to include the Tor binary!). Download and install again to fix.
Open-Source
What I’ve discussed so far is not that new. They’ve actually been around for a while, and they’ve been open-sourced for nearly as long.
That “open-source” thing is tossed around a lot, and often in totally bullshit ways.
All that “open-source” means is that the author has released the source code, the instructions they wrote to produce the software, for anyone and everyone to look at, use, adapt, and enjoy.
You have to teach yourself that particular programming language to use it, true, but you don’t have to depend on them telling you what their finished software does — you can build (and change) that software for yourself. Naturally, for any popular piece of open-source software there’s a community picking it apart to see if it breaks.
Proprietary or “closed-source” software, on the other hand, depends on you trusting the organization’s motives because they’re not about to share their “trade secrets” with you.
So it’s a choice between someone eager to share their work (in detail), and having equally eager people openly test it for stability and security — or what the corporation tells you is good for you. That’s how come open-source is so popular. It can be quirky — sometimes it takes a while to get used to a unique user interface and shortcuts — but it is, after all, made by individuals.
So what’s with open-source licenses? If you dig in, you realize that they actually turn the standard software licenses on their heads:
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without imitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
Translation: Our software MUST remain free for you to do with as you damn well please with one exception; we will sic copyright law on you if you try to claim exclusive ownership over it or its derivatives. If you want to sell this software, even as-is, then as long as you include the copyright notice we’re cool!
Sounds a little strange, even contradictory, but what it actually means is that while you’re free to profit off of open-source work (in most cases), you agree that it is open-source and that you will not violate other’s access to the same open-source material. What you do with that material, as long as you give a little nod via the license, is up to you — just as it is for others.
Now that’s a software license I can get behind.
Such licenses are all pretty much the same, more or less, and that same philosophy applies to non-software too (that little Creative Commons tag at the bottom of this site, for example).
And this model (giving stuff away for absolutely nothing), runs directly counter to every inbred economic instinct, and yet has proven to be profitable in very standard economic ways.
So now you have privacy, anonymity, and a some discretion in software (etc.) choices.
Now it starts to get interesting.
Cryptocurrrency
Many people have problems with this concept, so don’t feel bad if you have been labouring under the same misunderstandings.
When we talk about Cryptocurrencies, we often talk about one big example: Bitcoin, but there are quite a few more out there.
The “coin” part of the name is unfortunate because there are really no coins involved, electronic or otherwise. Bitcoin is more of a massive, peer-to-peer, public ledger into which transactions between individuals can be placed and verified. The BTC (Bitcoin) unit is simply a representation of worth to the parties involved, and the Bitcoin network makes it possible for these transactions to be done securely and honestly using strong cryptographic techniques.
Sounds kind of arbitrary, but it’s really not. Let’s say I decide that 1 BTC is $1. Do you agree with that? Great — when I want to send you payment for something, and we both agree that that something is worth $20, I’d send you 20 BTC. As long as I honour the BTC’s worth, you can then use it to exchange for another $20-worth of goods or services. Think of it as an IOU (which is basically what money used to be).
That’s fine for the both of us, but what if Bob down the street wants in on the action? Well, we can agree that $1 is 1 BTC, or maybe we can re-jigger our values to make it more accurate for all of us. So Bitcoin — the unit representation of community-derived worth — is more or less what people make of it. The Bitcoin network enables them to do that, and then use that agreed-upon “currency” for exchange.
This is a bit of a simplification, but that’s the gist of it.
Ultimately, using Bitcoin isn’t much more different than using money, and there are plenty of places where you can do exactly that. The transaction isn’t unlike using a debit or credit card in many ways, but the big difference is that you own your own account (usually stored on your device). If you lose access to it or someone hacks it, tough titties; it’s very much like cash in that way.
Bitcoin is pretty easy to integrate with Tor but needs a little help to be safely anonymous. Your Bitcoin wallet address might look like random data (and it mostly is), but without Tor and some additional protections, transactions may still be traced directly back to you, and with enough such information it’s feasible that you could be discovered. You may not think that selling good old-fashioned lemonade would bring the wrath of government down on you, but yeah, it will — they’ll fuck your life over good.
So protect yourself from these criminals as best as you can.
You may have read about some large Bitcoin and Tor-related site busts which, despite the rhetoric, were done using old-fashioned detective work — the technology remains pretty solid. Just don’t forget about the human part of the security and anonymity equation.
Keeping It Real
Having the ability to purchase physical goods and services using a cryptocurrency is great, but most likely those are going to be delivered via the government-owned post office. “And why exactly do you need all these lemons, Mister Bay?”
Unfortunately, it’s not looking like I’ll be able to replicate a bushel of lemons at home any time soon, but there are many real-world, physical objects which can be transferred digitally (and privately and anonymously), and reconstructed on increasingly cheap devices like 3D printers (and they’re not just for plastic trinkets). Star Trek-style gizmos, it turns out, aren’t that far-fetched.
Now do you suppose that with these nifty new 3D printers people will just stop everything and say, “Done! No more innovation!”? I doubt it.
Of course, this technology also has questionable applications, but these come with the territory.
We shouldn’t minimize the import of such uses, but we also shouldn’t focus unduly on what amounts to a drop in an ocean. We also can’t become complacent because the state is constantly working to put us under their thumb, but at the same time we shouldn’t get too paranoid about their capabilities.
There are many good people working hard to make all of this a reality. Some of those evil hackers that the teleprompter readers warn you about are some of the same people building these systems — you’ll need to discern for yourself what their true intentions are.
And that, ultimately, is what it comes down to … freedom. Conscious freedom to choose who you talk to, who you do business with, and to do what you want to do. Of course, with freedom comes responsibility, though most of us probably know that. If only government & friends could get a hint. But forget those fools because there are even more interesting things out there…